How to Check, Enable or Disable SMB Protocol Versions on Windows?
The Server Message Block (SMB) network protocol is used to share and access folders, files, printers, and other devices over network (TCP port 445). In this article, we will look at which versions (dialects) of SMB are available in different versions of Windows (and how they relate to samba versions on Linux); how to check the SMB version in use on your computer; and how to enable or disable the SMBv1, SMBv2, and SMBv3 dialects.
SMB Protocol Versions in Windows
There are several versions of the SMB protocol (dialects) that have consistently appeared in new Windows versions (and samba) :
- CIFS – Windows NT 4.0
- SMB 1.0 – Windows 2000
- SMB 2.0 – Windows Server 2008 and Windows Vista SP1 (supported in Samba 3.6)
- SMB 2.1 – Windows Server 2008 R2 and Windows 7 (Samba 4.0)
- SMB 3.0 – Windows Server 2012 and Windows 8 (Samba 4.2)
- SMB 3.02 – Windows Server 2012 R2 and Windows 8.1 (not supported in Samba)
- SMB 3.1.1 – Windows Server 2016 and Windows 10 (not supported in Samba)
In SMB network communication, the client and server use the maximum SMB protocol version supported by both the client and the server.
The summary table of SMB version compatibility looks like this. Using this table, you can determine the version of the SMB protocol that is selected when different versions of Windows interact:
| Operating System | Windows 10, Win Server 2016 | Windows 8.1, Win Server 2012 R2 | Windows 8,Server 2012 | Windows 7,Server 2008 R2 | Windows Vista,Server 2008 | Windows XP, Server 2003 and earlier |
| Windows 10, Windows Server 2016 | SMB 3.1.1 | SMB 3.02 | SMB 3.0 | SMB 2.1 | SMB 2.0 | SMB 1.0 |
| Windows 8.1, Server 2012 R2 | SMB 3.02 | SMB 3.02 | SMB 3.0 | SMB 2.1 | SMB 2.0 | SMB 1.0 |
| Windows 8, Server 2012 | SMB 3.0 | SMB 3.0 | SMB 3.0 | SMB 2.1 | SMB 2.0 | SMB 1.0 |
| Windows 7, Server 2008 R2 | SMB 2.1 | SMB 2.1 | SMB 2.1 | SMB 2.1 | SMB 2.0 | SMB 1.0 |
| Windows Vista, Server 2008 | SMB 2.0 | SMB 2.0 | SMB 2.0 | SMB 2.0 | SMB 2.0 | SMB 1.0 |
| Windows XP, 2003 and earlier | SMB 1.0 | SMB 1.0 | SMB 1.0 | SMB 1.0 | SMB 1.0 | SMB 1.0 |
For example, if a client computer running Windows 8.1 connects to a file server with Windows Server 2016, the SMB 3.0.2 protocol will be used.
According to the table, Windows XP and Windows Server 2003 can use only SMB 1.0 to access shared folders and files. The SMBv1 is disabled in newer versions of Windows Server (2012 R2/2016). So, if you are still using Windows XP and Windows Server 2003 devices on your network, they won’t be able to access shared folders on the file server running Windows Server 2016.
If Windows Server 2019/2016 with disabled SMB v1.0 is used as a domain controller, then Windows XP/Server 2003 clients won’t be able to access the SYSVOL and NETLOGON folders on domain controllers and authenticate with AD.
You may receive the following error when trying to connect to a shared folder on a file server with SMBv1 disabled:
The specified network name is no longer available
How to Check SMB Version on Windows?
Let’s look on how to find out which versions of the SMB are enabled on your Windows device.
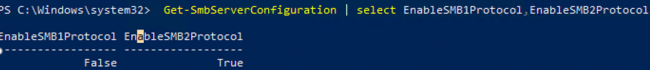
On Windows 10/8.1 and Windows Server 2019/2016/2012R2, you can check the status of various dialects of the SMB protocol using PowerShell:
Get-SmbServerConfiguration | select EnableSMB1Protocol,EnableSMB2Protocol
This command returned that the SMB1 protocol is disabled (EnableSMB1Protocol = True), and the SMB2 and SMB3 protocols are enabled (EnableSMB1Protocol = False).
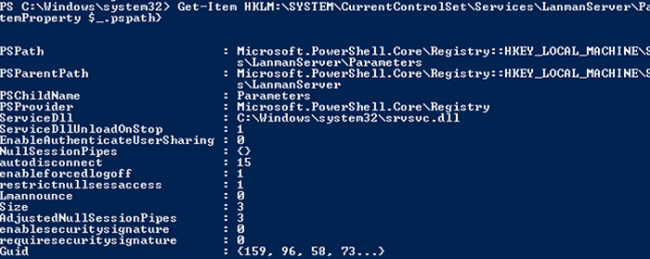
On Windows 7, Vista, and Windows Server 2008 R2/2008:
Get-Item HKLM:SYSTEMCurrentControlSetServicesLanmanServerParameters | ForEach-Object {Get-ItemProperty $_.pspath}
If there are no parameters named SMB1 or SMB2 in this registry key, then the SMBv1 and SMBv2 protocols are enabled by default.
Also on these Windows versions, you can check which SMB client dialects are allowed to connect to remote hosts:
sc.exe query mrxsmb10
SERVICE_NAME: mrxsmb10 TYPE : 2 FILE_SYSTEM_DRIVER STATE : 4 RUNNING (STOPPABLE, NOT_PAUSABLE, IGNORES_SHUTDOWN) WIN32_EXIT_CODE : 0 (0x0) SERVICE_EXIT_CODE : 0 (0x0) CHECKPOINT : 0x0 WAIT_HINT : 0x0
sc.exe query mrxsmb20
SERVICE_NAME: mrxsmb20 TYPE : 2 FILE_SYSTEM_DRIVER STATE : 4 RUNNING (STOPPABLE, NOT_PAUSABLE, IGNORES_SHUTDOWN) WIN32_EXIT_CODE : 0 (0x0) SERVICE_EXIT_CODE : 0 (0x0) CHECKPOINT : 0x0 WAIT_HINT : 0x0
In both cases, the services are running (STATE = 4 Running). This means that the current Windows device can connect to both SMBv1 and SMBv2 hosts.
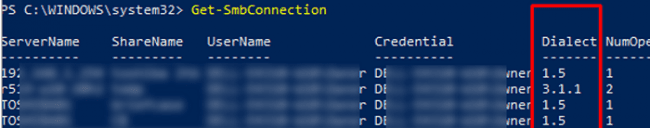
Checking Used SMB Dialects with Get-SMBConnection
When communicating over SMB, computers use the maximum SMB version supported by both the client and the server. The Get-SMBConnection PowerShell cmdlet can be used to check the SMB version used to access a remote computer:
The SMB version used to connect to the remote server (ServerName) is listed in the Dialect column.
You can display information about the SMB versions used to access a specific server:
Get-SmbConnection -ServerName srvfs01
If you want to display if SMB encryption is in use (introduced in SMB 3.0):
Get-SmbConnection | ft ServerName,ShareName,Dialect,Encrypted,UserName
On Linux, you can display a list of SMB connections and used dialects in samba using the command:
$ sudo smbstatus
On the Windows SMB server side, you can display a list of the versions of the SMB protocols that the clients are currently using. Run the command:
Get-SmbSession | Select-Object -ExpandProperty Dialect | Sort-Object -Unique
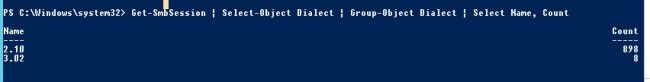 In this example, there are 898 clients connected to the server using SMB 2.1 (Windows 7/ Windows 2008 R2) and 8 SMB 3.02 clients.
In this example, there are 898 clients connected to the server using SMB 2.1 (Windows 7/ Windows 2008 R2) and 8 SMB 3.02 clients.
You can use PowerShell to enable auditing of the SMB versions used for the connection:
Set-SmbServerConfiguration –AuditSmb1Access $true
SMB connection events can then be exported from Event Viewer logs:
Get-WinEvent -LogName Microsoft-Windows-SMBServer/Audit
Stop Using the Insecure SMBv1 Protocol
Over the past few years, Microsoft has systematically disabled the legacy SMB 1.0 protocol in all products for security reasons. This is due to the large number of critical vulnerabilities in this protocol (remember the incidents with wannacrypt and petya ransomware, which exploited a vulnerability in the SMBv1 protocol). Microsoft and other IT companies strongly recommend that you stop using SMBv1 in your network.
However, disabling SMBv1 can cause problems with accessing shared files and folders on newer versions of Windows 10 (Windows Server 2016/2019) from legacy clients (Windows XP, Windows Server 2003), third-party OS (Mac OSX 10.8 Mountain Lion, Snow Leopard, Mavericks, old Linux distros), old NAS devices.
If there are no legacy devices left on your network that support only SMBv1, be sure to disable this SMB dialect in Windows.
If you have clients running Windows XP, Windows Server 2003, or other devices that only support SMBv1, they should be updated or isolated.
How to Enable and Disable SMBv1, SMBv2, and SMBv3 on Windows?
Let’s look at ways to enable and disable different SMB versions on Windows. We’ll cover SMB client and server management (they are different Windows components).
Windows 10, 8.1, and Windows Server 2019/2016/2012R2:
Disable SMBv1 client and server:
Disable-WindowsOptionalFeature -Online -FeatureName smb1protocol
Disable SMBv1 server only:
Set-SmbServerConfiguration -EnableSMB1Protocol $false
Enable SMBv1 client and server:
Enable-WindowsOptionalFeature -Online -FeatureName smb1protocol
Enable only SMBv1 server:
Set-SmbServerConfiguration -EnableSMB1Protocol $true
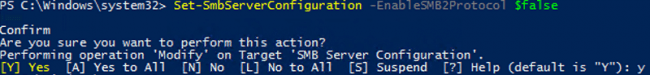
Disable SMBv2 and SMBv3 server:
Set-SmbServerConfiguration -EnableSMB2Protocol $false
Enable SMBv2 and SMBv3 server:
Set-SmbServerConfiguration -EnableSMB2Protocol $true
Windows 7, Vista, and Windows Server 2008 R2/2008:
Disable SMBv1 server:
Set-ItemProperty -Path "HKLM:SYSTEMCurrentControlSetServicesLanmanServerParameters" SMB1 -Type DWORD -Value 0 –Force
Enable SMBv1 server:
Set-ItemProperty -Path "HKLM:SYSTEMCurrentControlSetServicesLanmanServerParameters" SMB1 -Type DWORD -Value 1 –Force
Disable SMBv1 client:
sc.exe config lanmanworkstation depend= bowser/mrxsmb20/nsi
sc.exe config mrxsmb10 start= disabled
Enable SMBv1 client:
sc.exe config lanmanworkstation depend= bowser/mrxsmb10/mrxsmb20/nsi
sc.exe config mrxsmb10 start= auto
Disable SMBv2 server:
Set-ItemProperty -Path "HKLM:SYSTEMCurrentControlSetServicesLanmanServerParameters" SMB2 -Type DWORD -Value 0 -Force
Enable SMBv2 server:
Set-ItemProperty -Path "HKLM:SYSTEMCurrentControlSetServicesLanmanServerParameters" SMB2 -Type DWORD -Value 1 –Force
Disable SMBv2 client:
sc.exe config lanmanworkstation depend= bowser/mrxsmb10/nsi
sc.exe config mrxsmb20 start= disabled
Enable SMBv2 client:
sc.exe config lanmanworkstation depend= bowser/mrxsmb10/mrxsmb20/nsi
sc.exe config mrxsmb20 start= auto
You can disable SMBv1 server on domain joined computers by deploying the following registry parameter through the GPO:
- Key: HKEY_LOCAL_MACHINESYSTEMCurrentControlSetServicesLanmanServerParameters
- Name: SMB1
- Type: REG_DWORD
- Value: 0
Set the registry parameter SMB2=0 in order to disable the SMBv2 server.
To disable the SMBv1 client, you need to propagate the following registry setting:
- Key: HKEY_LOCAL_MACHINESYSTEMCurrentControlSetservicesmrxsmb10
- Name: Start
- Type: REG_DWORD
- Value: 4
Schannel
This is a Windows Server component used to provide identity security checking and authentication to enable secure, private communications through encryption. It relies on the cryptographic protocol in place. To ensure that Schannel uses TLS make sure these registry keys are set:
1. HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Control\SecurityProviders\SCHANNEL\Protocols\TLS 1.2
2. HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Control\SecurityProviders\SCHANNEL\Protocols\TLS 1.2\Client
“DisabledByDefault”=dword:00000000
“Enabled”=dword:00000001
3. HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Control\SecurityProviders\SCHANNEL\Protocols\TLS 1.2\Server
“DisabledByDefault”=dword:00000000
“Enabled”=dword:00000001
WinHTTP
WinHTTP provides a high-level server interface to the HTTP/1.1 Internet Protocol that applications and services running on Windows Server can use when establishing secure encrypted HTTPS sessions. Exchange uses it extensively. To ensure that WinHTTP is using TLS 1.2 make sure the following Registry keys are set:
1. HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\WinHttp
“DefaultSecureProtocols”:dword:00000a80
2. HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Internet Settings\WinHttp
“DefaultSecureProtocols”:dword:00000a80
.NET Framework
The .NET Framework is a core set of code libraries and runtimes that are used by many Windows Server-based services and Applications, including Exchange Server. It’s essential to ensure that the .NET Framework is using TLS 1.2 to encrypt and secure the many API points it provides and uses to communicate. To do this makes sure the following registry keys are set:
1. HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\.NETFramework\v4.0.30319
“SystemDefaultTlsVersions”=dword:00000001
2. HKEY_LOCAL_MACHINE\SOFTWARE\Wow6432Node\Microsoft\.NETFramework\v4.0.30319
“SystemDefaultTlsVersions”=dword:00000001
Client Machines
In addition to configuring all Exchange and other servers to use TLS 1.2, its vital that clients are also configurated to use the latest version so that clients communicate with Exchange Servers in the most secure and encrypted manner.